Welcome to Fintech Brainfood, the weekly deep dive into Fintech news, events, and analysis. You can subscribe by hitting the button below, and you can get in touch by hitting reply to the email (or subscribing then replying)
Weekly Rant 📣
🧠 Poor AML Will Ruin Stablecoins*
*If we don't figure out how to do it differently.
I work at Tempo and previously worked at Sardine. I have opinions and I have interests. I'll try to be fair, but I'm not neutral. That said, I pull no punches in this one.*
Every 4 years or so I write a eulogy for Crypto, in the hope that this time it learns the lessons of the last go around. I joke I'm the disappointed dad of crypto, having advocated for this space for a decade.
Well. Here we go again.

Don’t be defeated. We can make this stuff better.
The Conference Handshake
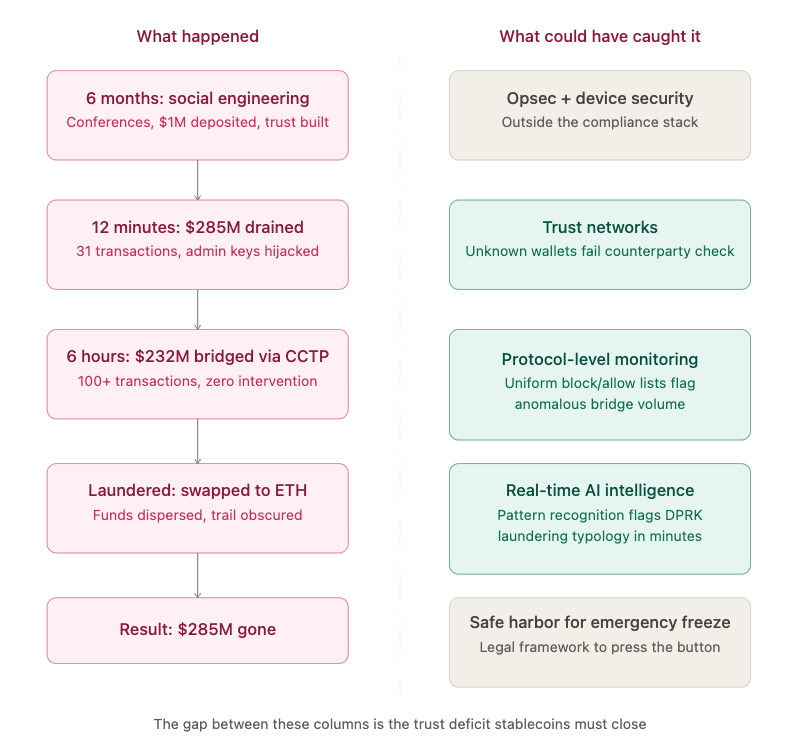
In the fall of 2025, a group of people approached Drift Protocol contributors at a major crypto conference. They said they were a quantitative trading firm. They wanted to integrate.
They were technically fluent. They had verifiable professional backgrounds. They were familiar with how Drift operated. A Telegram group was established. Over the next six months, they attended multiple conferences in multiple countries, meeting Drift contributors face to face, building working relationships, asking detailed product questions. Standard stuff for a trading firm.
In December, they onboarded an Ecosystem Vault on Drift. Deposited over $1 million of their own capital. They built a functioning operational presence inside the ecosystem. Deliberately. Patiently.
By the time April came around, these people weren't strangers. Contributors had worked with them for nearly half a year. Met them in person. Shared links to projects, tools, and apps they claimed to be building.
On April 1st, 2026, they struck. 31 transactions. 12 minutes. $285 million gone.
Yep, you guessed it, DeFi had another hack.
But the hack was DeFi. The laundering was of stablecoins. And the compliance failure lives in the gap between them.
After the exploit, the attackers' Telegram chats were scrubbed clean. The malicious software vanished. The investigation revealed the attack vectors:
A cloned code repository that compromised one contributor.
A TestFlight app presented as a wallet product that compromised another.
Possibly a known VSCode and Cursor vulnerability that was being actively flagged throughout winter — where simply opening a file was sufficient to silently execute arbitrary code. No prompt. No warning.
Elliptic and TRM Labs attributed the attack, with medium-high confidence, to UNC4736 — a North Korean state-affiliated group also tracked as AppleJeus or Citrine Sleet. The same actors behind the Radiant Capital hack in 2024. On-chain fund flows used to stage the Drift operation trace back to Radiant's attackers.
The people at the conferences weren't North Korean nationals. DPRK threat actors deploy third-party intermediaries for face-to-face operations. Fully constructed identities. Employment histories. Professional networks built to withstand scrutiny.
The most dangerous hackers don't look like hackers.
We're in April.
Stablecoins have product-market fit.
They're gaining institutional momentum. And my fear is the security and compliance gaps could kill them.
The Stablecoin Opportunity is Real
I've spent the last 18 months and tens of thousands of words making the positive case for stablecoins. There's a massive amount to be excited about.
We have an actual law the GENIUS Act, the first major piece of new financial services legislation in 15 years. The OCC, Treasury and Fed have all started to issue new guidance and opened request for comments on proposed rules.
We have product market fit. Artemis estimates that of the $35 trillion or so of stablecoin settlement, around $390bn is end-user payment flows for remittances, payroll, and corporate treasury.
Western Union, Ramp, Nubank and Revolut have all begun to roll out stablecoin acceptance, payments or capabilities to their 100s of million+ user bases
And the promise is even bigger than the cross-border settlement use case for non-G20 currencies. True, instant, global, 24/7 settlement. This happens today in some countries, some of the time (e.g., the ECB’s TARGET2.) Consider, however, that FedWire is 23x6, and cross-border settlement involving multiple correspondent banks can take 1 to 3 days.
This increasing legitimacy is drawing real interest from Wall St to Main St, and back again. Every major bank, clearing house and payments network is now looking at how stablecoins either compete with, or enhance their capabilities. Every corporate treasury team is salivating at the idea of true, instant cash positioning.
We have a long way to go before we get there.
And I can't escape the gnawing fear that the industry is sleepwalking into the one thing that could set it all back a decade.
Three Failures, One Problem
The Drift hack is one story. But it landed in the same week as two others.
$420 million in alleged compliance failures across 15 cases since 2022, where the US-regulated stablecoin issuer was slow to act or didn't act at all on illicit funds. Including the Drift hack itself, where $232 million in stolen USDC transited Circle's own bridge for six hours with zero intervention.
Sanctions compliance failures continue to surface across the ecosystem.
Iran's IRGC facilitation networks moved $3 billion through crypto last year.
Binance is back under DOJ scrutiny for sanctions evasion after its $4.3 billion fine.
The Russian ruble-backed A7A5 stablecoin processed $93 billion in under a year, purpose-built for sanctions evasion.
These look like separate stories. A hack. A freeze failure. Sanctions abuse. They're not. They're three failure modes on the same infrastructure, and they all point to the same underinvestment in trust.
Let me break them apart so we can put them back together properly.
Failure 1: The Drift Protocol Opsec Failure
Drift's problem was operational security against a state-sponsored adversary with military discipline and a six-month attention span.
North Korea's Lazarus Group has been at this since 2009. Sony Pictures. The Bangladesh Bank heist via SWIFT ($81 million, and they tried to steal $1 billion — a typo saved $920 million). WannaCry ransomware that shut down the NHS and paralyzed factories in 150 countries. Then they found crypto. Ronin Bridge, $625 million. Bybit, $1.5 billion. Now Drift, $285 million.
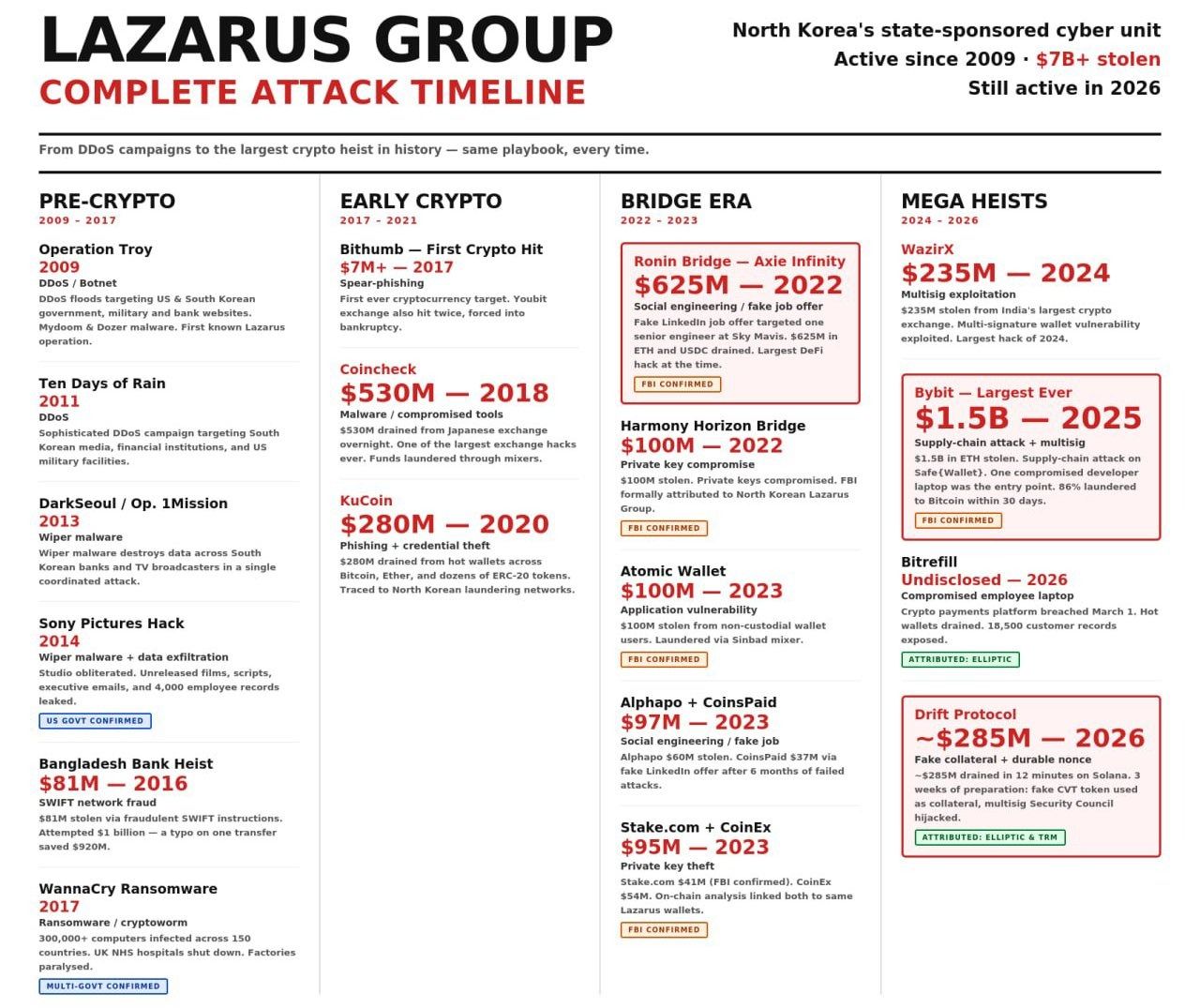
This is a consistent pattern
$7 billion stolen. Still active. Getting better.
None of this is unique to crypto — SWIFT had the Bangladesh Bank heist, the npm software supply chain just got hit too. If anything the issue is much worse, and much larger in TradFi. But crypto's transparency should make these flows catchable. That's what makes the failure to catch them so frustrating.
It’s a broader problem: this week North Korean hackers compromised the Axios npm package used by thousands of US companies for three hours, gaining access to deployment infrastructure across the software supply chain.
There’s a reason North Korea is on the sanctions list.
But risk is like whack-a-mole; you cut them off from the financial system, and they attack a different weak point. Crypto’s financial system. And like that, you’re back to money, finances, and money laundering and theft. Speaking of which.
Failure 2: The Attackers Used Stablecoins to Collect the Money
After the Drift theft, the attacker swapped stolen assets into USDC and bridged $232 million through Circle's own Cross-Chain Transfer Protocol. From Solana to Ethereum, through 100+ transactions. Over six consecutive hours. During US business hours.
Circle was unable to prevent it.
The Drift attacker held USDC across wallets for 1-3 hours before swapping. And deliberately avoided converting to Tether. They priced in Circle's response time and found it acceptable. This is an attacker who knows how your compliance ops work.
This sounds damning, but let me be fair about why this happens.
An active hack in progress creates ambiguous liability. What if the attacker mixed stolen and legitimate funds? What if Circle freezes the wrong wallets? There's no legal safe harbor for proactive emergency action on stablecoin issuers.
This is a systems and incentives problem, not a people problem.
Others in the security community are less charitable. They point out that Circle has the technical capability to freeze in minutes but routinely takes days or weeks, and that law enforcement has increasingly worked around Circle rather than through them. The pattern — citing privacy, citing legal process, citing decentralized principles — is a playbook borrowed from TradFi companies who found it operationally easier to be slow.
And Circle is one of the most reputable operators in this space.
US-regulated. NYSE-listed. State money transmitter licenses. Compliance marketed as their core differentiation. If it’s normal and even rational that a major actor has these gaps, ask yourself: what about the hundreds of stablecoin issuers and DeFi protocols with zero compliance infrastructure?
That’s my real fear.
Failure 3: The AML and Sanctions Failures are Endemic
Meanwhile, the broader ecosystem.
North Korea stole $2.02 billion in crypto in 2025. A 51% increase year-over-year. Cumulative DPRK theft now exceeds $6.75 billion. The US Treasury directly links these funds to the weapons of mass destruction program.
Iran's IRGC facilitation networks moved over $3 billion through crypto in 2025. IRGC-associated addresses accounted for more than half of all value received by Iranian services by Q4. The Russian ruble-backed A7A5 stablecoin — purpose-built for sanctions evasion — processed $93 billion in less than a year.
The individual companies here are not the point.
Threat actors exploit the weaknesses in the system, and right now stablecoins are a major weakness in the system. But surely, that shouldn’t be the case.
The Paradox of Transparency
If blockchains are transparent, how is this possible?
When you have a golden source of every transaction ever on a blockchain, your fincrime investigations become very different. You don't have to chase a paper trail through 3 or 4 correspondent banks. You don't have to call Singapore at 2am. It's all right there.
Circle has a freeze function baked into the USDC smart contract. They can blacklist wallet addresses. Their terms of service explicitly reserve the right to restrict access for suspected illicit actors "in its sole discretion."
The tools exist. The data exists. The authority exists.
And still: 6 hours. 100+ transactions. $232 million. Zero intervention. Business hours.
Stablecoins have a compliance superpower that tradfi never had. And the industry hasn’t figured out how to apply it to the 24/7 nature of the new tools.
We’ve begun to extract the benefits from the new payments rails, but without managing the risks. Sure, thats where we are in the cycle.
But this is me screaming into the void that the window to fix that is closing. Fast.
The obvious question: if we have the transparency and automation software, why not instant-freeze?
Freezing assets costs money and loses customers.
Every proactive freeze is a potential lawsuit. Congress is trying to address this gap. The upcoming CLARITY Act, Title III, Section 305, creates a 30-day safe harbor for issuer freezes, with the ability to be extended under certain criteria. The framework exists. The question is whether issuers will use it, and whether the implementing rules give them enough to act fast.
The problem is compliance is still seen as a cost center, not a revenue center. And the 24/7 monitoring infrastructure needed to catch a 6-hour bridge window isn’t given CEO-level focus until there’s a disaster. (And it’s not that expensive)
Circle's behavior during the Drift hack isn't irrational. It's exactly what you'd expect from a public company navigating ambiguous legal exposure in real time.
If we want different outcomes, we need to change the system.
And we have a window, because the regulatory rules for GENIUS are still in their comment period.
That starts with not copying tradfi's homework.
Don't copy-paste TradFi’s compliance.
The temptation after reading all of this is to conclude that stablecoins need the same AML policies, procedures, and controls as banks.
Sure, they can learn from those best practices (and there are plenty). But there’s also a lot to learn from how to do it better. TradFi doesn’t have a great rep here:
False positive rates in AML monitoring routinely exceed 90%.
The average bank takes 95 days to complete KYC due diligence. That's increasing.
Major banks average 307 employees dedicated to KYC alone.
Banks paid $56.1 billion in AML-related fines in the last decade.
BNP Paribas: $8.9 billion. TD Bank: $3 billion. The fines keep coming and nothing changes.
AML catches less than 0.1% of criminal finances globally. I described this years ago as the world's most ineffective policy experiment. Imagine if you had a car that didn't work 99.9% of the time.
Even the regulators are signaling the old approach isn't working. This week FinCEN published a notice of proposed rulemaking that explicitly encourages financial institutions to adopt machine learning, GenAI, and blockchain analytics in their AML programs. FIs won't incur additional risk solely for using these tools, and innovation in AML programs can weigh in the bank's favor during enforcement reviews.
The worst possible response would be to bolt this onto stablecoins. It would destroy the properties that make them better infrastructure — speed, cost, programmability — while still failing to catch the actual bad actors.
The answer is different. Use the properties that make stablecoins different to build compliance that actually works.
Some Ideas for What We Can Do Better
There are three layers to this, and the industry needs all of them.
Layer 1: Trust Networks
Notabene started as a Travel Rule compliance layer for crypto. It's becoming something much more interesting: a trust network. Known wallets. Known counterparties. Shared reporting. This new capability is early, but promising. This messaging layer lets you extend trust and operate in pockets of light (you could do the same with SWIFT, EWS, other regional networks etc).
Wider data sharing (beyond travel rule) would mean wallets receiving stolen USDC would have been flagged before they could move funds.
We also need a policy solution.
CLARITY Section 305 already provides a 30-day safe harbor for issuer freezes. The framework exists — but the implementing rules need to give issuers enough clarity and confidence to act in minutes, not days.
The industry should be actively engaging the comment process to make this work.
Layer 2: Protocol-Level Compliance
There's a tension in the stablecoin stack. We want the base layer to be neutral. Open. Censorship-resistant. That's the whole point.
But AML requires the ability to block, freeze, and report. And right now every stablecoin issuer implements this differently with custom smart contract code. This means attackers get to exploit the known gaps per issuer.
We can build uniform compliance primitives at the infrastructure level so they're consistent and predictable. For example at Tempo we're baking block/allow lists into the blockchain’s native stablecoin contract standardn.
Tempo memos also can link to ISO 20022 UETRs, so your existing reporting infrastructure can trace a stablecoin payment end-to-end in the same format you use for SWIFT. (Yes, that's a deliberate wink to the transaction bankers reading this. And to every other blockchain, to adopt these features too.)
Standardization is useful. It forces us to think about best practices. Combine the protocol-level controls with a trust layer, and you can then start to build a real-time compliance and data function around that.
Layer 3: Data and Intelligence
My experience at Sardine taught me something I keep coming back to: all risk problems are data problems.
Onchain, we have good data; if we can share it through trust networks in a standard way, we can then apply real-time intelligence to that data.
The problem is humans don’t work 24/7. Agents, however, do.
Vendors like Sardine and Beacon are building AI agents with fincrime expertise baked in. You can hire that expertise now rather than trying to build it with a team of hundreds, and it could be responding in real-time to these threats.
Layer 4: Being default real-time in compliance.
If you build 24/7, instant-settlement, global payments infrastructure, your compliance infrastructure has to be 24/7, instant, and global too. Batch processing won't cut it. 9-to-5 compliance teams won't cut it.
The Drift attacker knew Circle's response time and priced it in. That confidence — that unhurried six hours — is the most damning indictment of the status quo I've seen.
AI and Agents allow you to have 24/7 responses of human quality. Every day the attackers get faster, sped up by AI tools. We have to get faster too.
I Want to be the Proud Dad of Stablecoins
What drives me is that we can make things better. We have agency.
Yet every time, crypto has these giant, public, humiliating moments. Every time, the space loses credibility it spent years building. And every time, the potential is still there. Still real. Still enormous.
Tokenization is real. Very here. Very mainstream. Stablecoins have crossed from "experimental" to "institutional." But we have to build the trust infrastructure to match the payment infrastructure.
The blockchain gives us a compliance superpower that the correspondent banking system never had. Real-time visibility. Single global ledger. Programmable rules. We just have to actually use it.
The only question is whether the industry invests in trust as seriously as it invests in throughput.
I think it can. I've seen what these teams can build.
I'm just disappointed it's taking this long.
ST.
4 Fintech Companies 💸
1. Catalog - AI Product discovery for Merchants
Catalog connects merchant SKU data to the sources used by AI to discover products. It connects to a merchants existing back end, and will publish (and republish) updates as they’re added every 15 mins, 12 or 24 hours.
🧠 The one bit of agentic commerce we know is working is product discovery. People are researching products in LLMs. It’s a new channel and as a merchant, you need to be there.
Zalos - Agents for Finance Ops
Zalos provides agents that can work with existing portals, ERPs and software stacks to automate reconciliation, download payslips and statements. Every click, screen and key entry is audited for human intervention.
🧠 This is targeted at enterprises that have workflows and dashboards that will not be replaced any time soon. Their providers won’t be rolling out new AI features, so it makes sense that AI displaces labor not software.
3. Worth - SMB Onboarding and Underwriting Automation
Worth helps companies consolidate multiple PDFs and systems into a single, branded onboarding and underwriting platform for customers and internal staff.
🧠 Getting closer to the truth in lending is the key to good underwriting. Worth differentiating on “crosswalking” technology, which uses Google, IRS, and dozens of sources to provide “the industry’s most accurate data.” The website almost hypnotizes you with the word revenue. Revenue. Revenue. Bob Dole. (Yes, that’s a Simpson’s reference)
4. Payy - A blockchain for private stablecoin transactions
Payy promises zero fees on stablecoin transactions, privacy on any ERC20 (stablecoin-like) transfer, through “high performance” Zk Proof network which is “EVM compatible.” Meaning little to no change for wallet. They also offer a Payy card. The website says 10m transactions have completed since launch.
🧠 Privacy is the new meta in stablecoin land (just look at Visa becoming a supervalidator on Canton, for example). Payy is leaning into that, with a card and a wallet. They’re in a competitive market for chains, but the direct distribution with a card might allow them to bootstrap volume.
Things to know 👀
Revolut launched its AI assistant called "AIR" that can take actions mid. chat. AIR rolled out in the UK last week and takes actions inside the chat thread like blocking a recurring payment, buying an eSIM for your next trip or breaking down what you spent in Spain last summer.
🧠 AI chatbots used to be annoying, now they’re useful and good. Custom tool calls make them able to take action. An AI that can find subscriptions you’re missing and cancel them is much more useful than a read-only one.
🧠 The insight here is to create custom tool calls on your own modified open-weight LLM. Every bank right now is trying to build a custom foundation model for underwriting. But doing that for customer service and then adding tool calls for your app functionality is a much higher impact move than just taking one of the generic customer service AI companies' products.
🧠 But the UX question is unanswered to me. Why would a user choose the chat function? And if they did, would they know what to prompt? Most people stare at an LLM and don’t know what to say. Is that true in a finance agent too?
🧠 The agent is also trapped inside the app. It can do useful things but only on that account. That’s probably a good thing. This is the same pattern Public is using. But long term surely the answer is something that sees all of my apps
Perplexity Computer is their personal agent. Their secure version of OpenClaw. Perplexity Computer now connects to your bank accounts, credit cards, loans, and brokerage through Plaid. You can ask it to build a budget, a debt payoff plan, or a net worth dashboard. Done in seconds, across ANY account that connects to Plaid.
🧠 Within hours of launch, Twttier abcdabcd987 user claimed it helped them save $14k on their taxes that their $2,000 CPA missed. (Checked and double checked manually after).
🧠 75% of Perplexity's paying users already ask it finance questions monthly. Plaid is the obvious best way to enrich that data, in a secure way. There’s user demand here. OpenClaw is hard to set up; Perplexity Computer isn’t. It’s a solid home.
🧠 I think chat is SUCH a better interface for understanding money vs charts in a PFM. In conversation can ask rich, natural language questions, build plans and implement them. This is nearing that personal RIAA style conversation. That then pulls up charts only when needed.
🧠 How long now until Perplexity Computer can take action on your behalf? It’s obviously limited by security concerns and then, what Plaid can action. But consider that Ramp launched a CLI, and many Neobanks have APIs. The most agent-friendly banks will win the next decade.
🧠 I sometimes wonder if Perplexity is just doing consumer R&D for everyone else to copy or if it is durable. But I also believe the future of consumer AI use is multi-model, not single.
Good Read
Bad B2B content has a tell. It opens with a question nobody has once asked. In today’s fast-moving landscape, how do you stay ahead? It uses the word “leverage” as a verb. It has an unreadable section called “Key Takeaways.” It treats the reader like someone who showed up to be educated rather than someone who showed up because they already have a problem and need to think it through
🧠 Slow clap. No notes. I literally laughed out loud several times. The most enjoyable, laser-guided missile of truth you’ll read this week. Stop reading my crap and read Cokie instead. And then subscribe. And then etch the words in stone.
Tweets of the week 🕊
That's all, folks. 👋
Remember, if you're enjoying this content, please do tell all your fintech friends to check it out and hit the subscribe button :)
Want more? I also run the Tokenized podcast and newsletter.
(1) All content and views expressed here are the authors' personal opinions and do not reflect the views of any of their employers or employees.
(2) All companies or assets mentioned by the author in which the author has a personal and/or financial interest are denoted with a *. None of the above constitutes investment advice, and you should seek independent advice before making any investment decisions.
(3) Any companies mentioned are top of mind and used for illustrative purposes only.
(4) A team of researchers has not rigorously fact-checked this. Please don't take it as gospel—strong opinions weakly held
(5) Citations may be missing, and I’ve done my best to cite, but I will always aim to update and correct the live version where possible. If I cited you and got the referencing wrong, please reach out

